If you were wondering what is the WPS (Wi-Fi Protected Setup), know that it is a network security standard created by the WiFi Alliance in 2006 as an alternative to the regular means of adding devices to the network, so, instead of requiring the user to insert the SSID (WiFi network name) and the passkey, it relies on various other methods, such as a PIN, on NFC, the Push button or USB to significantly simplify the device pairing process.
This means that the WPS’s reason of existence is simplicity and user friendliness, but it was also a reaction to the independent development of similar solutions by the major manufacturers (and we all know how much the developers like walled garden – this way, the WPS remains non-proprietary and universal). Not to delve too much on the history, the WPS was created out of necessity, but, as it has been discovered a few years after its launch, this feature has proven to be problematic on the long run.
The statistics show that about 90% of the people in the US had access to the Internet in 2019, and things got better since then so it\s safe to assume that almost every home now has a router to allow wired and wireless devices to connect to the network. This indicates that people got a lot more familiar with the networking devices and the wireless router/access point is no longer that weird industrial-looking piece of equipment that only a select few knew how to handle. That’s a consequence in part because of the continuous process of simplification of the software, but also due to the growing popularity of the Internet.
How is WPS implemented on Linksys routers?
The WPS allows the user to simply undergo the initial configuration wizard to personalize some aspects of the network, such as the admin account and the SSID + password (on some routers, you don’t really have to, but you still should do it for security reasons), while the WPS is not necessarily going to be a part of the setup wizard, but it will always remain there as that strange button (or software option) that, along with some other advanced features, will most likely remain ignored by the user (while some will simply feel intimidated by it). Let’s take the good ol’ Linksys WRT3200ACM as an example.
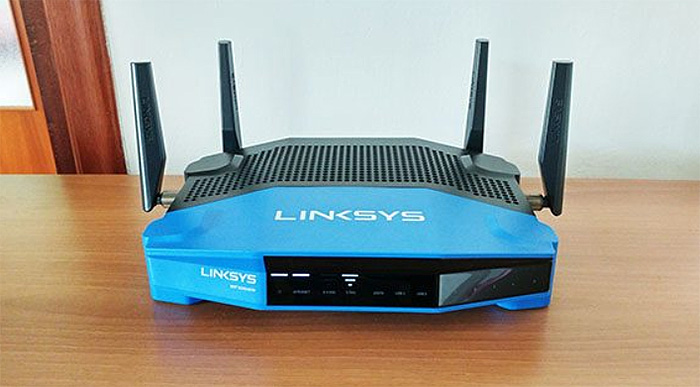
The router has the WPS button positioned next to the four Ethernet LAN ports (the first available button from the left) and in order to get a better understanding about how it works, I opened the web-based interface and, under Router Settings > Wi-Fi Settings, I clicked on the WiFi Protected Setup (WPS).
Here, I noticed a large switch that enables or disables the function (this will activate or deactivate the physical button as well) and, underneath it, Linksys offers three methods: the first is the Push Button which requires that you push the WPS button on the compatible client and then on the router (this way the WRT3200ACM will automatically detect and pair with the client.
You do have about two minutes to press the button on the second device. The next method is the Router PIN which prints a number that you have to enter on the client device and lastly, there’s the Device PIN, where you enter the PIN number generated by the client to quickly pair the two devices.
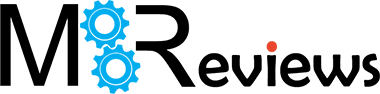
How is WPS implemented on WiFi 5 Asus routers?
As you can see, the WPS feature works in a similar manner using an Asus router (specifically, the Asus RT-AC86U).
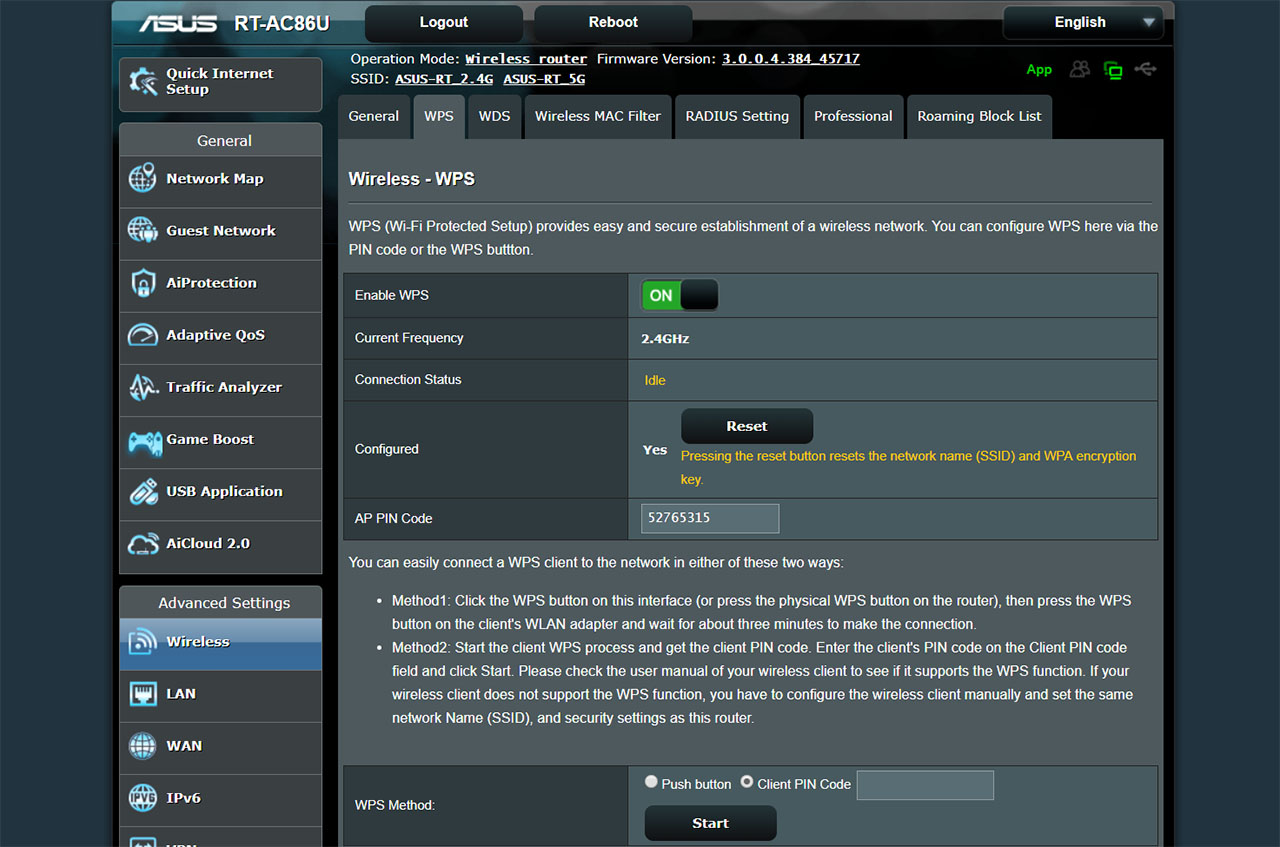
This highlights one of the available implementation of the WPS: the Push Button method which only enables the WPS for about two minutes (the time limit when the pairing can occur) and, while the WRT3200ACM and the RT-AC86U has a physical button, some routers will have a virtual switch which will work in a similar manner – this is the case of the TP-Link Deco M9 Plus, which allows the user to access the WPS feature directly from the main menu of the app (under the Router Settings). It’s worth noting that most (if not all) routers that have a WPS button will also provide a LED indicator which will let you know when the pairing process has been initiated, usually through a pulsating light.
Note: The WPS works only with devices that support WPA or WPA2 encryption type and it will not work with devices that still use the old WEP encryption type (please don’t use devices that have this encryption because they’re very vulnerable to exploits).
What about on mesh systems?
With the rise of the WiFi mesh systems, the manufacturers have stripped the traditional router of some buttons and functions to make it more digestible for the general public. So, in most cases, the WPS button is gone (replaced by the virtual button as can be seen on the Deco M9 Plus), but there are manufacturers that removed this function altogether (such as Google WiFi and Eero).
I also noticed that the WRT3200ACM lacks the WPS window if you install the OpenWRT (Project LEDE) custom firmware, so, why did that happen? To answer this question we have got to go back to 2011, when Stefan Viehböck discovered that the WPS PIN number was vulnerable to brute-force attacks and, in some cases (depending on the router), even if the user would disable the WPS function, the device would still remain in a vulnerable state.
To fix this many manufacturers have released patches that would either allow the user to completely disable the WPS or to time-out the pairing process in case a brute-force attack was detected. The next blow to the WPS function came in 2014, when Dominique Bongard talked about the Pixie Dust attack, which, once again was able to take advantage of the way the WPS process functions, so it could recover a part of the security code when the router would communicate with the client and part of it by using a brute-forcing attack – it is limited to only a few chipset makers, specifically MediaTek, Realtek, Ralink and Broadcom.
So, while the PIN number method is vulnerable, does this issue affect the Push button method as well? It’s tempting to think that the short period of time when the button activates the WPS process could render this method more secure, but, unfortunately, the WPS requires that the PIN method to be implemented (it’s mandatory), so the device still remains in a vulnerable state.
If everything suggests that WPS leaves your network vulnerable, why do people still want to use it?
You’d be surprised, but there was some outcry when Google decided to not include WPS into the feature set of the Google WiFi and when the Android Pie OS didn’t support it, so there are people out there that want this feature to remain in their devices and the reason for that is simplicity. The technology evolves to offer us (the users) a better and more simple way to do things and, a recent example is the app-only UI available on some minimalist WiFi systems that got more popular than the difficult-to-configure interface from the industrial-looking router.
Some tech-savvy people will object, but the large majority of users has fully embraced this new trend (and that’s not a bad thing). So why shouldn’t we keep on adding a printer to the router without dealing with long passkeys, since WPS made things so simple and intuitive? Unfortunately, this is one of those times when we have to get back to a previous, less intuitive way of doing things simply because security should be the top priority of every person that has access to the Internet.
I know that the necessity of security may seem abstract on a home network and one may wonder, why would a hacker target me? The better question is why not? For example, your network can be used for illegal activities, such as downloading copyrighted material or a lot worse (this case is an interesting read) or your router can become a part of large-scale attacks against various websites, institutes or organizations (and I’m sure you keep on hearing on the news about these attacks that often cripple businesses).
So what can you do to remain secure? First of all, make sure that your router is updated to the latest firmware available (if the manufacturer hasn’t released an update in a long time, maybe it’s time to search for a better option); next, make sure that your WiFi network has a personalized password and that it is long and strong enough (use various characters to make it more difficult) and lastly, disable WPS completely (this can be done from the user interface) – some routers don’t give the user the option to do so (yes, even high end ones) and, in this case, make sure that at least the firmware has protection against brute-force attacks.
How is WPS used in 2023?
Let’s take the Asus GT-AX6000 as an example. The wireless router is a part of the WiFi 6 standard, so it has all the bells and whistles of the commercial modern networking hardware.
But it still has a WPS button on the front which serves the same function as it did almost two decades ago. Is it more secure? It’s exactly the same as it was on the old Asus RT-AC86U, so not much has changed over the last five years in regard to the WPS, even if we’ll soon get WiFi 7 wireless routers.
References:
1. Wi-Fi_Protected_Setup & Vulnerabilities
2. How is WPS supposed to work?

Mark is a graduate in Computer Science, having gathered valuable experience over the years working in IT as a programmer. Mark is also the main tech writer for MBReviews.com, covering not only his passion, the networking devices, but also other cool electronic gadgets that you may find useful for your every day life.