Lastly, there’s the Maintenance section where you can access the Diagnostics to Copy the diagnostic files to a USB storage, run the Packet Capture utility or the Network Tools (includes Ping IPv4 and Traceroute IPv4). And that’s all the standalone UI has to offer, so let’s register the NSG50 to the Nebula Cloud to use it as it was intended. To access the Nebula Cloud, enter http://nebula.zyxel.com and log into your account or create a new one (the wizard will guide you through the creation of a new organization and site).
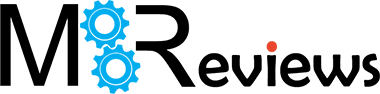
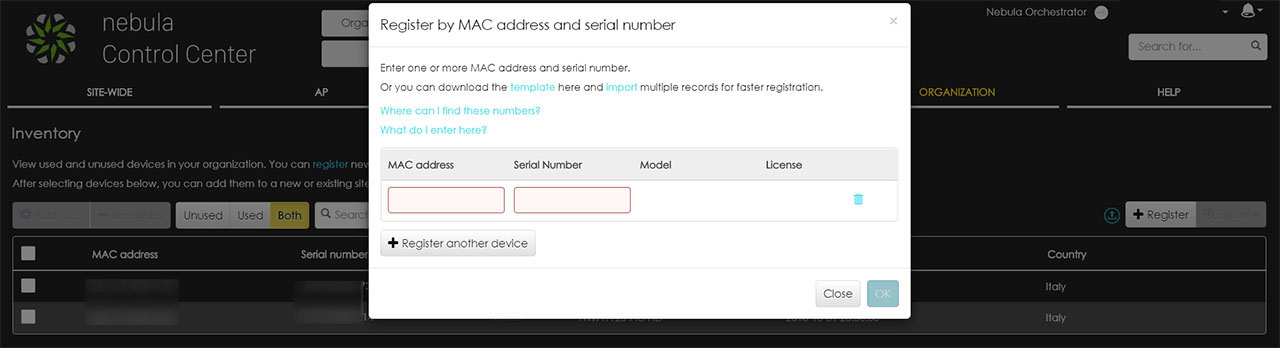
After gaining access to the nebula Control Center, go to Organization and, under Configure, select Inventory: here, you’ll be able to see a list of all already registered devices and, by clicking on the ‘+Register’ button, you will summon a small window, where you will have to enter the MAC address and the Serial Number of the NSG50 (this info can be found on the bottom of the device). After adding the gateway, you will have to Add it to your site (press the button on the left called ‘Add to’).
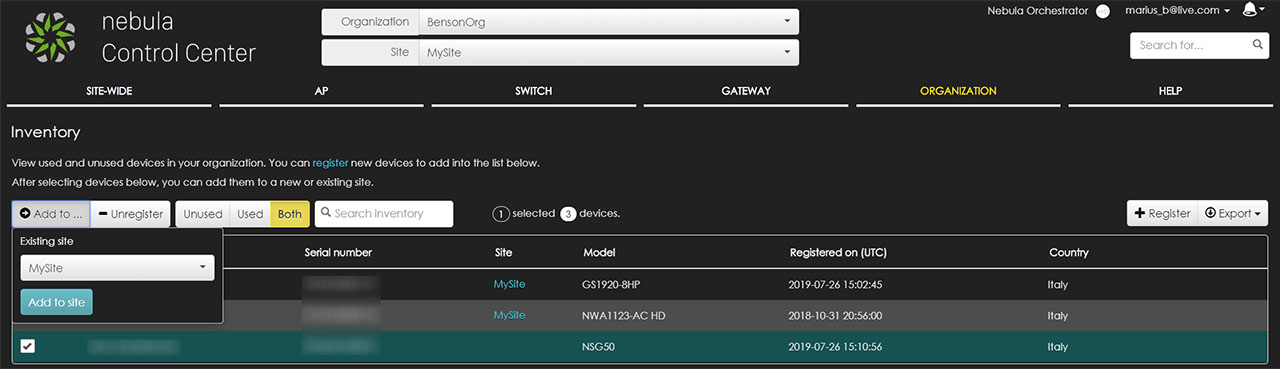
When returning to the Dashboard, you will be able to see all those newly populated areas: under Gateway, there’s the total amount of Online gateways, while under the WAN Throughput, you can see the upload / download throughput for each WAN and, towards the right, there are two other dedicated areas, one for the Traffic Summary (Internet Usage and Top Applications) and the other for the Top Gateway Clients.
Using the main menu (which is positioned horizontally), we can navigate to the Gateway section which, when clicked, will summon a small window divided by Monitor and Configure. Under Monitor, you can view details about your Security gateway, including the location on the Map, a graphical representation of all the ports, as well as live graphs for the Internet traffic, the Network usage and connectivity – there are also some Live tools, such as Ping, Traceroute and DNS (as well as the ability to Reboot the gateway remotely).
Still under Monitor, you can view the Client activity and a list of all the connected clients (each displaying a set of tags) – if you click on any client, it will display more detailed info about the device and a graph with the upload and download stats (displayed over specific periods of time).
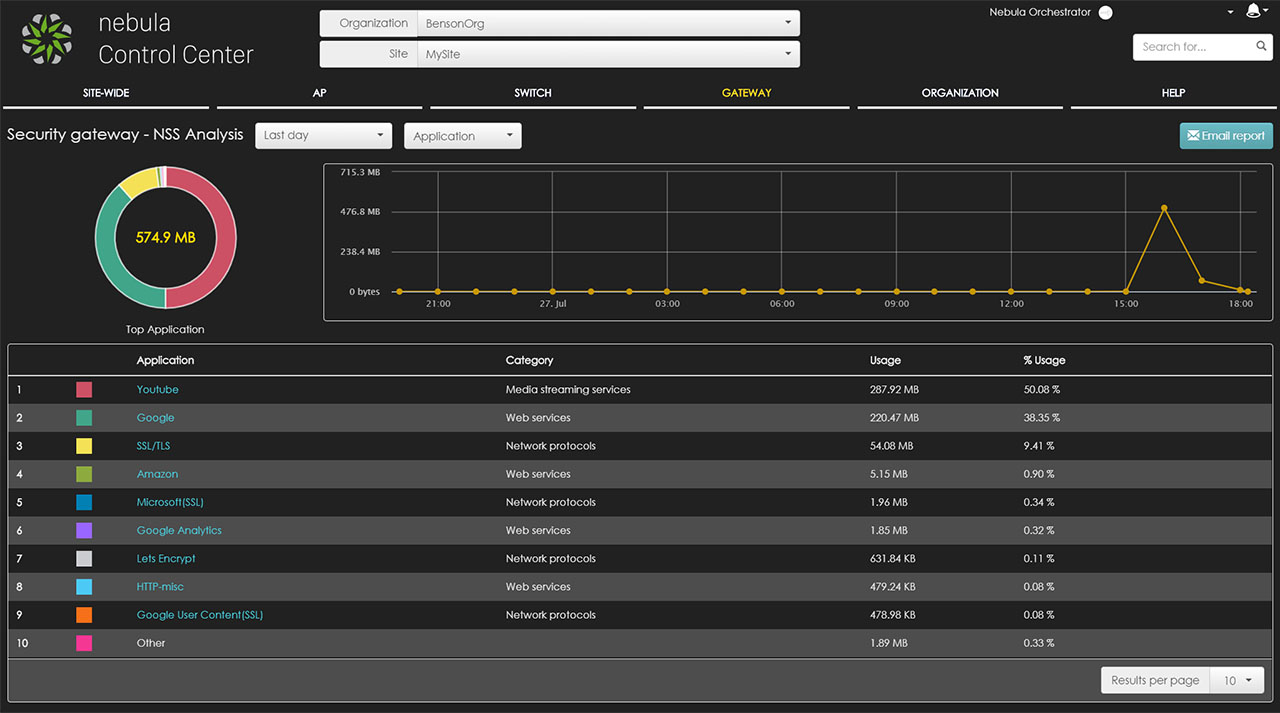
Underneath the Client section, there’s the Event log, the VPN connection (status, site and L2TP Login Account), the Nebula Security Service NSS Analysis (shows detailed analysis report about the Antivirus, the Content Filtering and the Application – it’s in Beta state) and the Summary Report (shows the WAN1, WAN2 and VPN usage, as well as other stats such as the Top apps by usage or Clients per day). Besides the Monitor area, under Gateway, there is also the Configure group of options which includes the Interface addressing, where you can select between NAT or Router as the Network Mode, you can create two separate groups of ports to isolate them from possible threats and that can be later assigned to a VLAN interface – you can also add Static Routes or enable the DDNS.
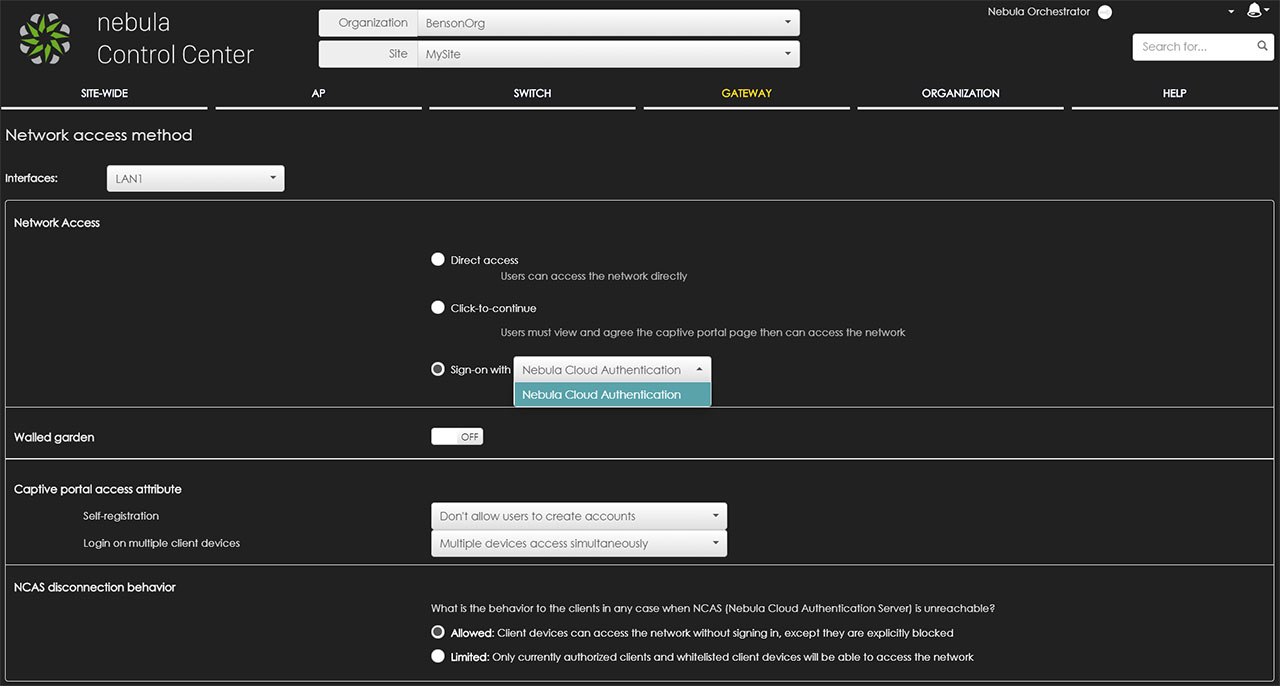
Furthermore, you can also configure the Firewall, where you can add Outbound rules, enable the Application Patrol, create Schedule profiles (which will be used by the Outbound rules) and configure the 1:1 NAT mappings as well as the Virtual Server mappings for web modules, but be aware that the Application Patrol and the IDP services only come with a one year license. Underneath the Firewall, there’s the Policy Routing section, the Content filtering (where you can set a deny access message, as well as a Redirect URL, add a Black/White list and block certain Categories – it includes Parental Control, Productivity, Security or Custom Templates), Site-to-Site VPN, L2TP over IPSec client and the Network access method (Direct access, set a captive portal before access or Sign on using the Nebula Cloud Authentication – includes enabling the Walled garden, allowing users to create accounts with manual or auto authorization, how many devices can have access simultaneously and set what happens when the Nebula Cloud Authentication Server becomes unreachable).
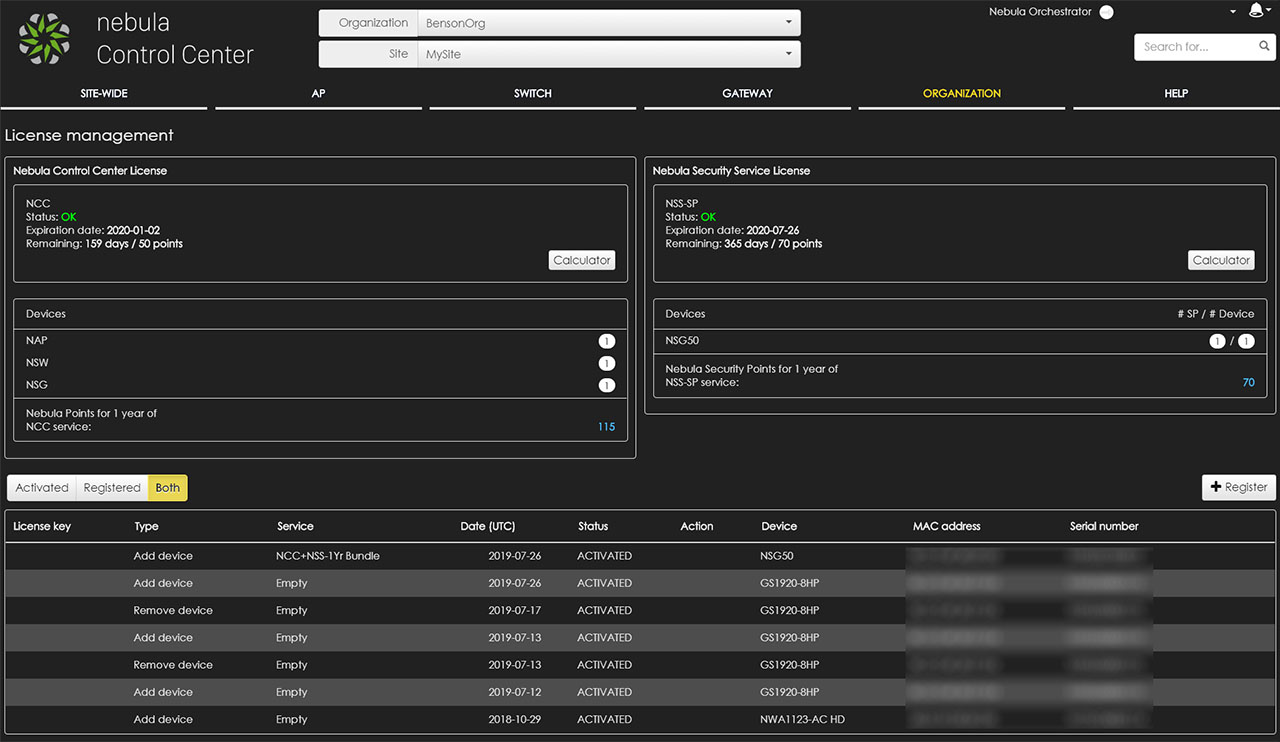
Further down, there’s the Walled garden configuration policy, the Captive portal (the splash page that can appear when accessing the Internet – it can be assigned to either of the two LAN groups), the Traffic shaping (dual WAN feature, the Global bandwidth limit and the Session Control), the Security filtering (includes the IDP and the Antivirus configuration) and the Network Servers (DNS and Authentication Server – can be AD Server or RADIUS Server). To renew the licenses, you need to go to the Organization section (from the main menu) and select the License management which will display all the current active licenses.
If you return to the Site-Wide main section and choose the Summary report, you can see additional info regarding to the gateway, such as graphs with live traffic on both WAN ports, the Map and floor plan which will allow you to easily see all the deployed devices even if they’re on different sites and the Topology which displays your network ‘circuit’. To upgrade the firmware of the NSG50, you need to go to the Configure group of options and select the General Settings > Firmware upgrades: you can schedule the upgrade or upgrade the firmware now. Still under the Configure group, you can set various alerts (when the DHCP lease pool is exhausted, when a VPN connection initiates or stops or when the WAN connection status has changed) or view the status of the firmware under the Firmware management section.
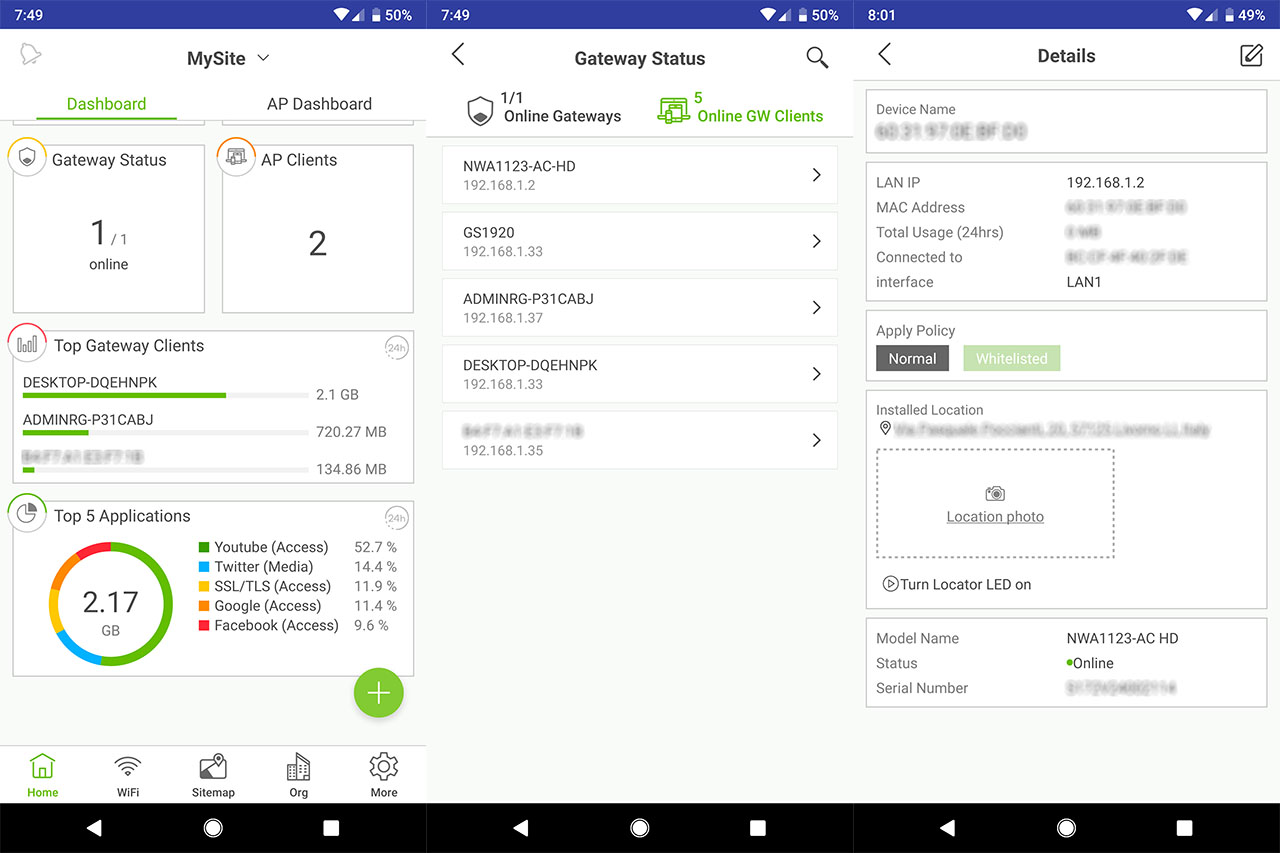
The Zyxel network can also be managed using the Nebula app which, similarly to the web-based UI, will show you the organization and the site that you have configured and, after you added the NSG50 security gateway, it will show various stats on the Dashboard (the top clients and the top applications) and it will also allow you to configure the connected clients (including applying access policies), so it is significantly more limited than the web-based interface, but it will be enough for remote site surveillance.
This is the first Cloud managed gateway that I have tested in depth, so I can’t yet compare it with other devices specific to other controllers (such as the UniFi compatible gateways), but, I can say that but I was surprised by how easy it is to configure various aspects about the network – that is, after I got more familiar with the interface (one negative is that there isn’t enough documentation for each possible application).
Conclusion
Due to their versatility, the Cloud controllers have gotten really popular in the SMB market and Zyxel does offer an appealing case for how such a solution should be implemented. The Nebula Cloud is clearly more mature than the Linksys controller, the Open Mesh CloudTrax or the TP-Link Omada controller and, while it’s still a behind the UniFi, the developers constantly add new features and the manufacturer has made the Nebula Cloud Center almost entirely free. The NSG50 is an optimal security gateway for smaller businesses capable of delivering a decent performance while also keeping the network safe from any type of threats, but, just like with the other Zyxel devices, you need a bit of time to get familiarized with all the options on the Cloud Center and where to find them (there is a learning curve) and I’m still waiting for some storage-related options to be implemented. Still, it’s a great gateway solution, borrowing a lot of options from the excellent USG series, so you can’t go wrong with the NSG50 if you intend to give the Zyxel environment a try.
Zyxel NSG50
Pros
- Remote management and monitoring using Nebula Cloud Center
- Security features: Antivirus, Firewall, IDP, VPN and more
- Good thermal performance
- Good integration with the other Zyxel devices (WAPS and Etherent Switches)
- Nebula app (iOS and Android OS)
Cons
- There are no storage related features on the NCC
- The NCC requires a bit of a learning curve

Mark is a graduate in Computer Science, having gathered valuable experience over the years working in IT as a programmer. Mark is also the main tech writer for MBReviews.com, covering not only his passion, the networking devices, but also other cool electronic gadgets that you may find useful for your every day life.