The ZYXEL USG FLEX 200HP is a part of the recently-released USG FLEX H series, this particular model being aimed at SMBs, having a special focus towards providing better security without having an impact on the throughput and overall performance.
| ZYXEL USG FLEX 200HP | |
|---|---|
| Zyxel.com | Check Product |
I have tested the entry-level USG FLEX 100 and there are some clear improvements across almost the entire spectrum. When compared to the FLEX 200, the ZYXEL USG FLEX 200HP offers a better SPI, VPN, UTM and ISP throughput, so there is little penalty when running security-related features and the developers have also introduced the uOS which should make the interaction with the device faster.

As expected, a lot of the aforementioned features are Cloud-based and ZYXEL did give into the latest AI fad, opting to use what it calls AI-powered Cloud intelligence for IPS, sandboxing and more. And, considering that the impact on the throughput is far less than before, I’d say it may have paid off. But, it’s not all software optimization because the ZYXEL USG FLEX 200HP does have better hardware than its predecessor, as we will see in the teardown section, but it does go farther than that, including a 30W PoE+ port which can be useful for adding one wireless access point.
Considering the major advances in networking tech, the ZYXEL USG FLEX 200HP must have some multi-Gigabit ports, right? Indeed, it does, there are two 2.5GbE ports and if you need to go up to 10GbE, then the flagship USG FLEX 700H model does have a couple of them. That being said, let’s test the ZYXEL USG FLEX 200HP and see how it performs.
Design and Build Quality
SMB firewall gateways usually follow a simple design where the case is rectangular, so it’s easy to mount them in a rack. They look very much different from the consumer-based wireless router. The case of the ZYXEL USG FLEX 200HP is metallic and that includes the front section as well, but it is worth mentioning that the manufacturer has added some decorative plastic elements.

And, if you’re familiar with previous iterations, you’d know that the red accents are a design characteristic for the USB series for almost a decade. It does look nice and helps it stand out from other brands. The ZYXEL USG FLEX 200HP is slightly larger than the entry level 100HP, measuring 10.7 x 7.36 x 1.42 inches (or 27.2 x 18.7 x 3.6cm) which does make it easier to be mounted in a rack without the need to use a tray. Of course, we do get mounting ears in the package, as well as four silicone feet to add to the bottom in case you decide to leave the gateway on a desk or shelf.
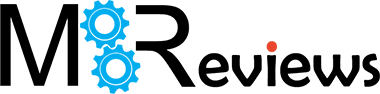
Furthermore, the ZYXEL USG FLEX 200HP is fairly heavy, so there is no chance that it would budge even if you make use of all the available ports, just make sure to add the silicone feet. As for the heat management, as you will see in the next section, ZYXEL did add a couple of large heat dissipation plates which push the hot air out and, as expected, there are no fans, so we’re dealing with passive cooling. Still, it’s a fairly powerful device and yes, there are lots of heat vents all around the gateway, but are they enough?
I did take some thermal photos of the ZYXEL USG FLEX 200HP while it was under a fairly high load and you can see the result for yourself. Now, let’s talk about the ports and connectors. Despite seemingly very rack-friendly, the Power port is positioned on the rear side, alongside the grounding screw. As for the front side, let’s start from the left. We get three LEDs, one showing that the ZYXEL USG FLEX 200HP is powered on and that there’s traffic passing through, the other lights up when you use the PoE port.
Lastly, there’s the User LED which stays solid green when the admin is logged in, flashes green if the license is expired and gets solid amber if the user is locked out. Underneath the LEDs, we can use the two recessed buttons to Restart and Reset the gateway. To the right, we get USB-A port which is followed by a couple of LEDs for the P1 and P2 ports. These are the two 2.5GbE Ethernet ports and the second one which is marked with yellow, it’s the POE port (802.3at that goes up to 30W).

The other six ports are Gigabit Ethernet, while the last RJ45 port is for the Console connection (we do get a VGA to Ethernet cable into the package).
The ZYXEL USG FLEX 200HP Teardown
After paying a hefty sum on any electronic device, you do have the right to maintain and even repair it, so I decided to see how easy it is to reach the inner components and whether ZYXEL dislikes people poking inside the gateway. The first thing that needs to be done is remove all the screws on the side of the ZYXEL USG FLEX 200HP, as well as from the rear panel. And then, the metallic top piece should come out, right? Well, it didn’t in my case, so I poked around with the prying tool, but no luck.
And then I remembered that ZYXEL really likes to put those warranty void stickers which shouldn’t mean anything in front of the law. So yeah, there was an extra screw. After that, the top panel could easily be removed and we can see a fairly large metallic plate which guides the heat away from the PCB.
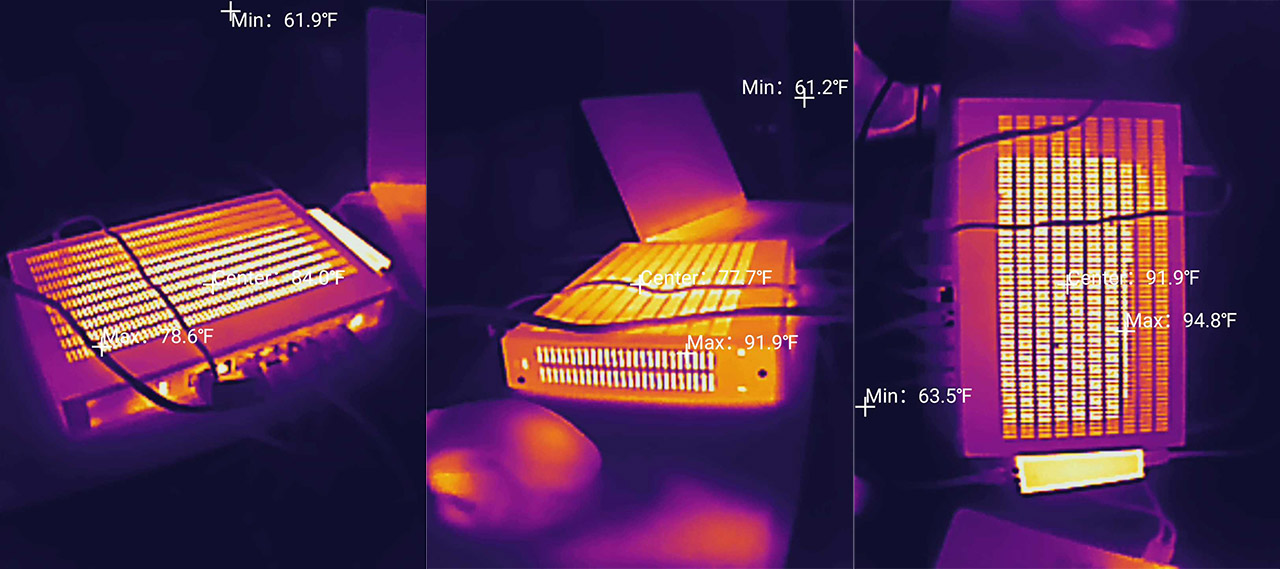
I removed that as well and then I wanted to take the PCB out completely. Be aware that it’s an easy process because it’s held into place by a metallic protrusion from a screw I previously removed. Carefully move around it and it should come out. I saw a smaller metallic plate also used for heat dissipation as well as the main components. There’s the quad-core Marvell ARMADA 7050 CAT72 SoC (88F7-BVQ4) based on the ARMv8 CPU clocked at 1.4GHz.
| EnGenius ESG510 | TP-Link TL-ER7206 | ZYXEL USG FLEX 200HP | ZYXEL USG Flex 100 | |
| CPU | quad-core 1.6GHz Intel ATOM E3940 X236F668 | dual-core 880MHz CPU (probably Mediatek) | quad-core 1.4GHz CPU (Marvell ARMADA 7050 CAT72) | dual-core 1.2GHz Cavium Octeon III CN7020 |
| RAM | 4GB Samsung (2x SEC 219 K4FGE3S4HMMGCJ) | 512MB Samsung SEC 204 K4B2G16 | 8GB Samsung (8x SEC 301 K4A8G085WB-BCTD) | 2GB Nanya 1922 NT5CC512M8EN |
| Storage | 8GB SEC 231 8041 KLM8G1GETF | 128MB ESMT F59L1G81MB | 8GB Samsung (SEC KLM8G1GETF) | 8GB Kingston EMMCC08G-M325 |
| Switch | 4x Intel S2353L34 | Realtek RTL8367S | 2x Marvell 88E2111-BWS4 | Qualcomm QCA8337 |
Then, I could see the two Marvell 88E2111-BWS4 single-port 2.5GbE PHY for the dedicated Ethernet ports and 8GB of eMMC 5.1 storage memory from Samsung (SEC 304 B041 KLM8G1GETF). Lastly, I could identify the 8GB of RAM from Samsung (8x SEC 301 K4A8G085WB-BCTD) – four chipsets on each side.
The Installation
ZYXEL decided to use a different subnet for the new USG series, so, after connecting a client device to the ZYXEL USG FLEX 200HP, you need to go to 192.168.168.1 and, when prompted, enter admin and 1234 for the username and password.
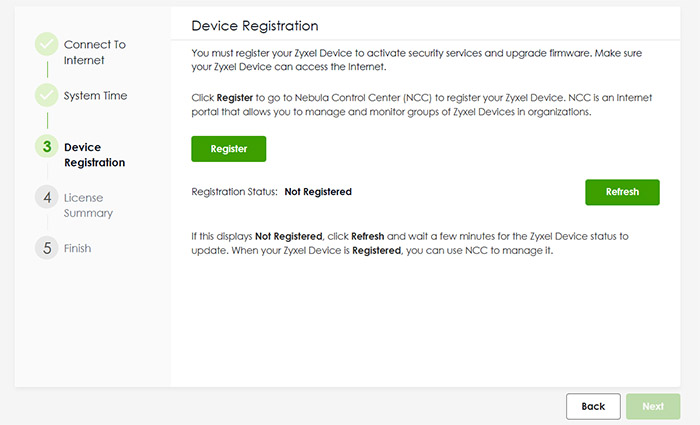
On the next step, you can enter a new password, but the username remains admin, so that needs to be changed afterwards. Zyxel will also ask the user to agree with their terms and Privacy Policy, and when using the Cloud features, pretty much all the data that’s entering the servers will be collected (including activity logs). After that the wizard asked that I register to the Nebula Control Center without giving me the option to skip it, so it’s mandatory when using this device.
This will take use to the myzyxel site where it’s necessary to create a new account (or log into a new one) and then, you can create a new Organization and Site. Since the USG Flex 100 was already the gateway of a previously-used site, I decided to keep using the same Organization, but create a new site. Well, the website agreed with me that I should create a new Site, but it just didn’t allow me to do so. I had to create an entire new Organization which is idiotic because an Org can have multiple Sites.
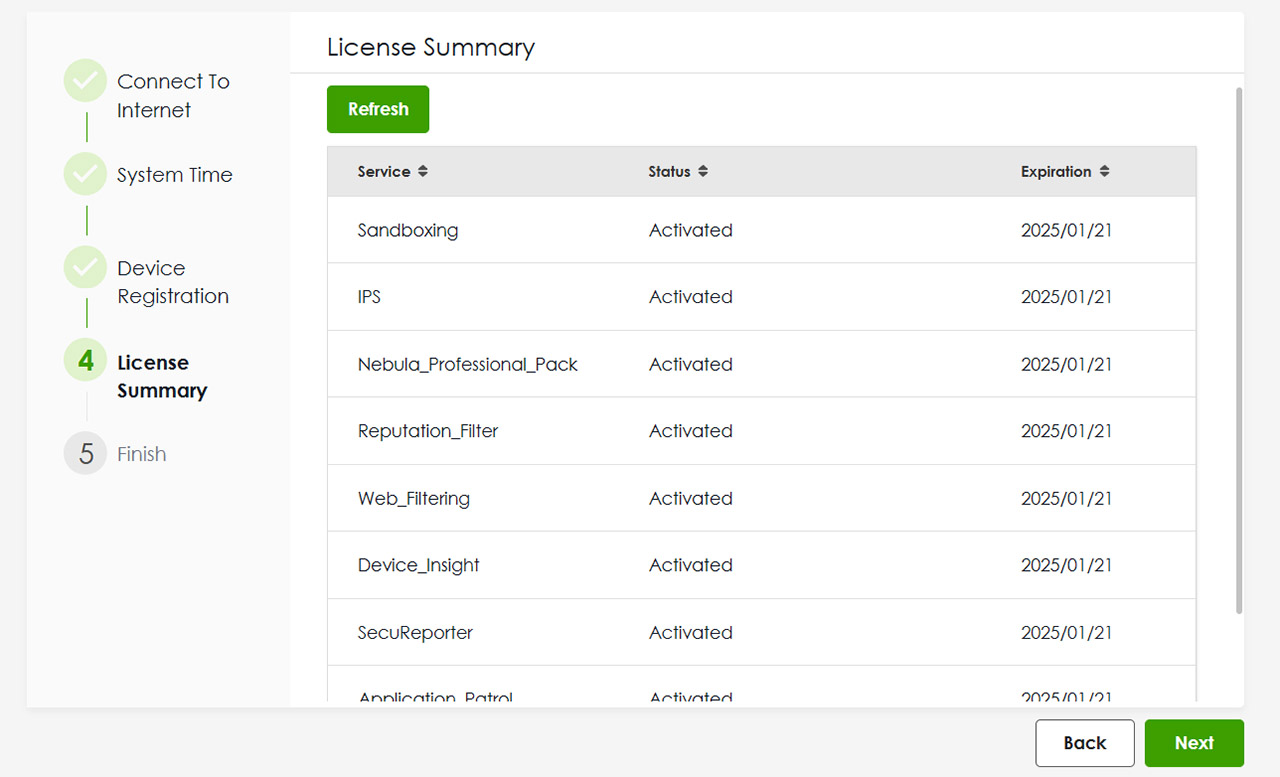
Anyway, the ZYXEL USG FLEX 200HP was quickly detected and I could finally register the gateway. After that I could see all the Services that are Activated, as well as the Expiration date (some of the services do need to be renewed). And that’s about it, we can now access the local management platform.
The Local Management Platform
Although you will get the most out of the firewall gateway when it’s connected to the Cloud, ZYXEL has made available a very comprehensible local management platform. The first window that you’re going to visit is the Dashboard which shows some general status info about the System or about the Security features that are running in the background. This includes DNS and URL threat filter, the Anti-Malware, Sandbox and IPS scans. There is also a dedicated System Statistics where you can see per-port data, as well as some hardware-related functionalities.
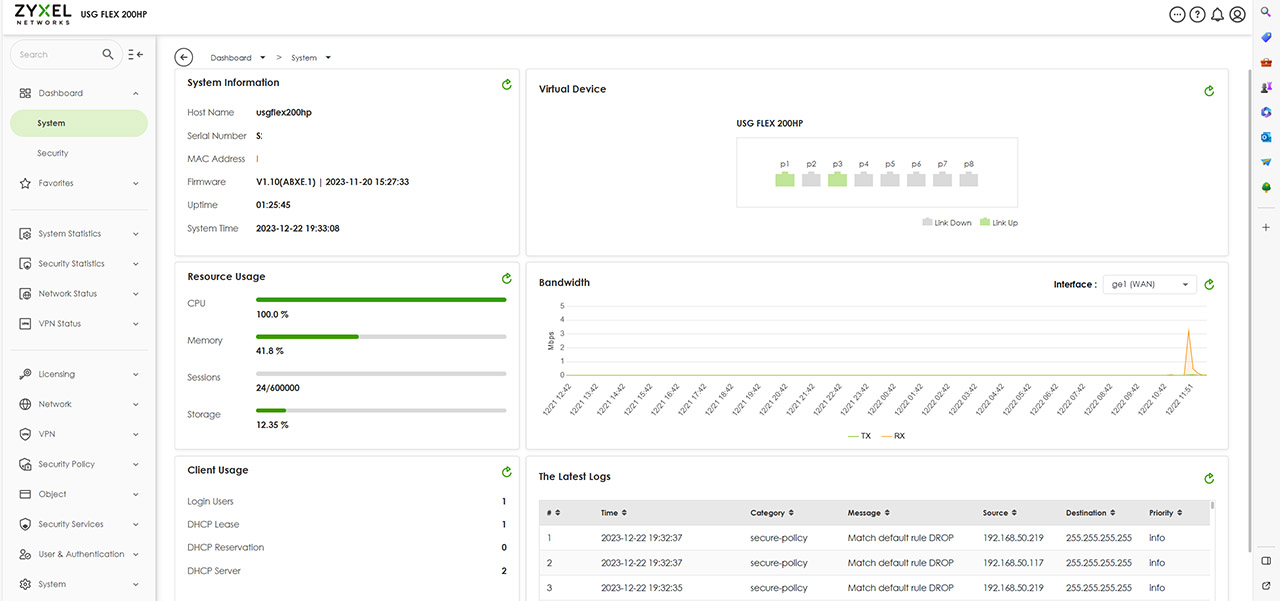
The aforementioned Security status info can go far more in depth under the Security Statistics and it includes a few other options such as the App Patrol, the Content Filter and the SSL Inspection. The last two sections under this particular group will show detailed data about the Interface and the VPN (IPSec and SSL). Under the next group of settings we get the Licensing which shows that there is some communication with the Cloud since everything that has been enabled there can be used locally as well.
Then, we get access to the Network area and it’s under the Interface that we get to adjust the way the ports will behave – and yes, we will immediately test how good is the dual-WAN implementation. Under VPN, there are only two options available, the IPSec for site-to-site connection and the SSL VPN which can work with the SecuExtender client, but it’s also compatible with OpenVPN Connect clients. Further down, we can change or create new Security Policies and Objects, while under Security Services, it’s possible to adjust each feature in great detail.
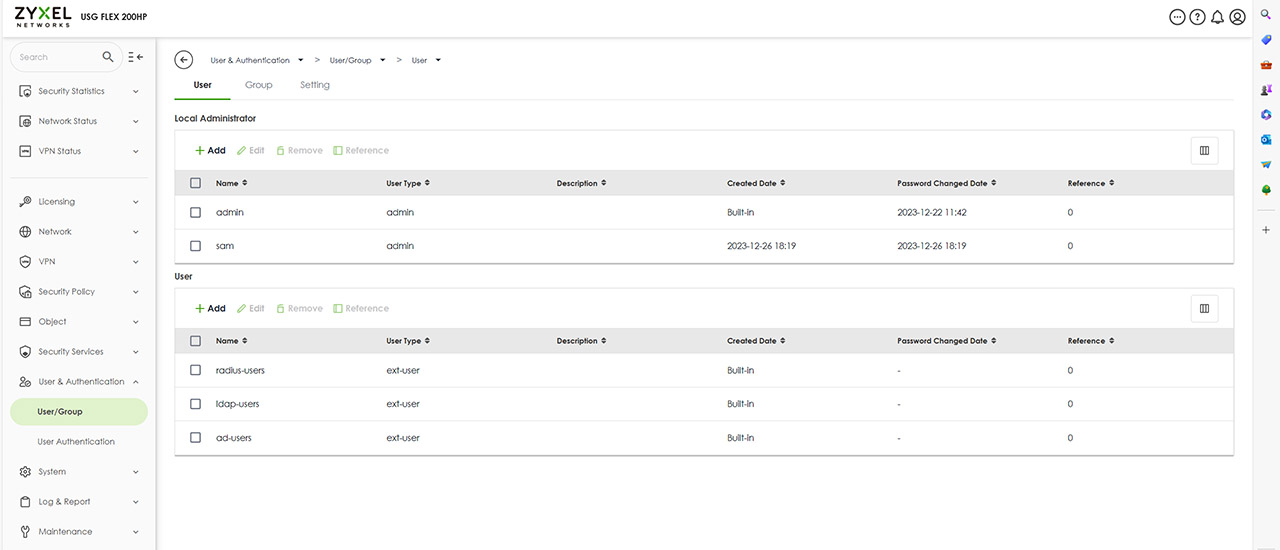
The next important section is the User & Authentication where it’s possible to create new users, including administrators and I did try to get rid of the admin username account for security purposes, but I couldn’t which is great.. I also need to mention the Maintenance section which has some cool Diagnostics tools that include the Packet Capture technique, as well as Network Tools (NSLOOKUP, PING and TRACEROUTE).
The Security Services
I am not going to go very in-depth about every feature, but I do need to mention that under the Content Filtering, it’s possible to create Profiles or use the default ones (Business Productivity Protection or Children’s Internet Protection). Also, under the Reputation Filter, you can choose which types of outside threats will be blocked, as well as those from the LAN (botnets). You can also create an Allow and Block list.
The Anti-Malware offers a very high level of control, allowing the user to choose what happens with the infected files, the type of files that will be scanned, add File Name Patterns, MD5 Hashes and more. Under IPS, you can choose between the Prevention and the Detection mode (can’t run both at the same time since it can become a resource hog).
Dual-WAN and Load Balancing
While the FLEX 100 has a single default WAN port, with the option to use a secondary port as WAN, the ZYXEL USG FLEX 200HP is more forward with its multi-WAN capabilities, sporting two WAN ports from the get-go. This means that connecting both WAN ports Internet sources (a couple of modem) will automatically populate the Network > Interface > External section. On the next step, we could go to Trunk and choose a different type instead of the Default one, but I noticed that there is a single type available: Weighted Round Robin.
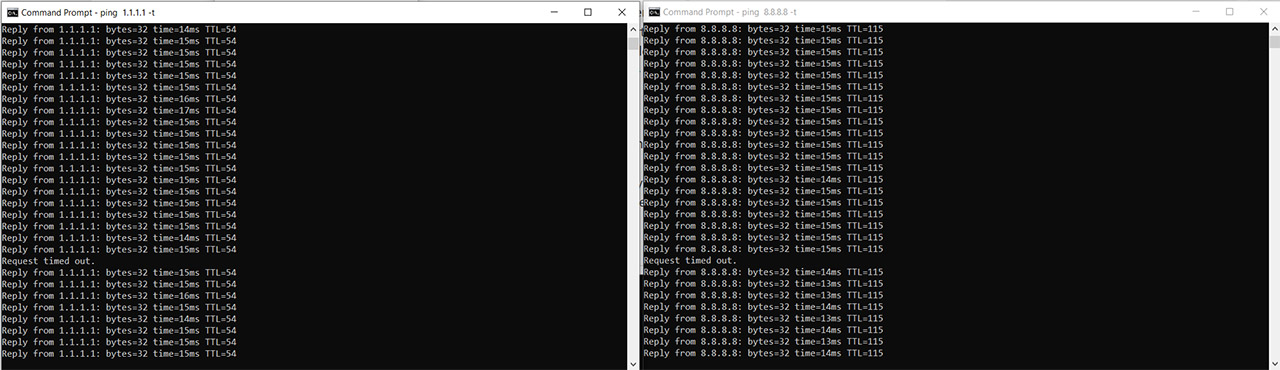
Yes, even the default one uses it, so I didn’t make any changes for this specific test, since I didn’t need to. All I wanted to check was how quickly the ZYXEL USG FLEX 200HP switches to the secondary WAN link after the first being disconnected and then how quickly the first reconnects after going back live. I pinged 1.1.1.1 and 8.8.8.8 continuously at the same time, made sure that both links were active and I disconnected the first WAN cable.
As you can see, both pings experienced single Request time out and then resumed their communication. After reconnecting the main link (the cable to the first WAN port), the same thing happened again. So, you can expect a timeout of a single second.
The Stress Test
While I haven’t done this before with other dual-WAN security gateways, I did run a few stress tests on some consumer-level routers, so I decided that it would be interesting to see how well the ZYXEL USG FLEX 200HP manages to handle multiple demanding client devices. I could always just run a single iperf instance, but would that reflect real-life behavior? Not really. The test suite that I use is the net-hydra which has netburn at its core (all developed by Mr. Jim Salter and available for free).
The client devices that I connected are diverse and I would have liked to use multiple identical computers, but they’re expensive, so I can only use what I have available. The server computer has the following specs:
- WiFi 6 built-in adapter + 2.5GbE Ethernet port
- 32GB RAM
- NVMe SSD storage
- AMD Ryzen 5 5600xt
- Radeon RX 6800xt.
The five client devices have the following specs:
| 2x Lenovo Y520 | Custom PC | MacBook Pro | ZimaBoard 832 SBC | |
| Ethernet Adapter | Built-in Realtek adapter | Built-in Realtek adapter | QNA-UC5G1T 5GbE adapter | Ethernet Adapter Intel I225 adapter |
| RAM | 16GB | 16GB | 8GB | 8GB |
| Storage | NVMe SSD | SSD | NVMe SSD | SSD |
| CPU | Intel i7-7700HQ | Intel i5 5600K | Intel Core i5 | Intel Celeron Apollo Lake N3450 |
| GPU | GTX 1050ti GPU | NVidia GT720 | Intel Iris Graphics 540 | Intel HD Graphics 500 |
The first test simulates the streaming of 4K videos on all five clients at the same time. This means that the throughput is limited at 25Mbps, a value that has to be reached on every client device and, ideally, there should be very little latency. Unlike the WiFi tests, we should get better results since the connections are wired, but you will see some interesting behaviors depending on the Ethernet adapter. We want the latency to remain lower than 100ms at all times, although some would argue that even 150ms can be passable before the user gets annoyed by buffering.
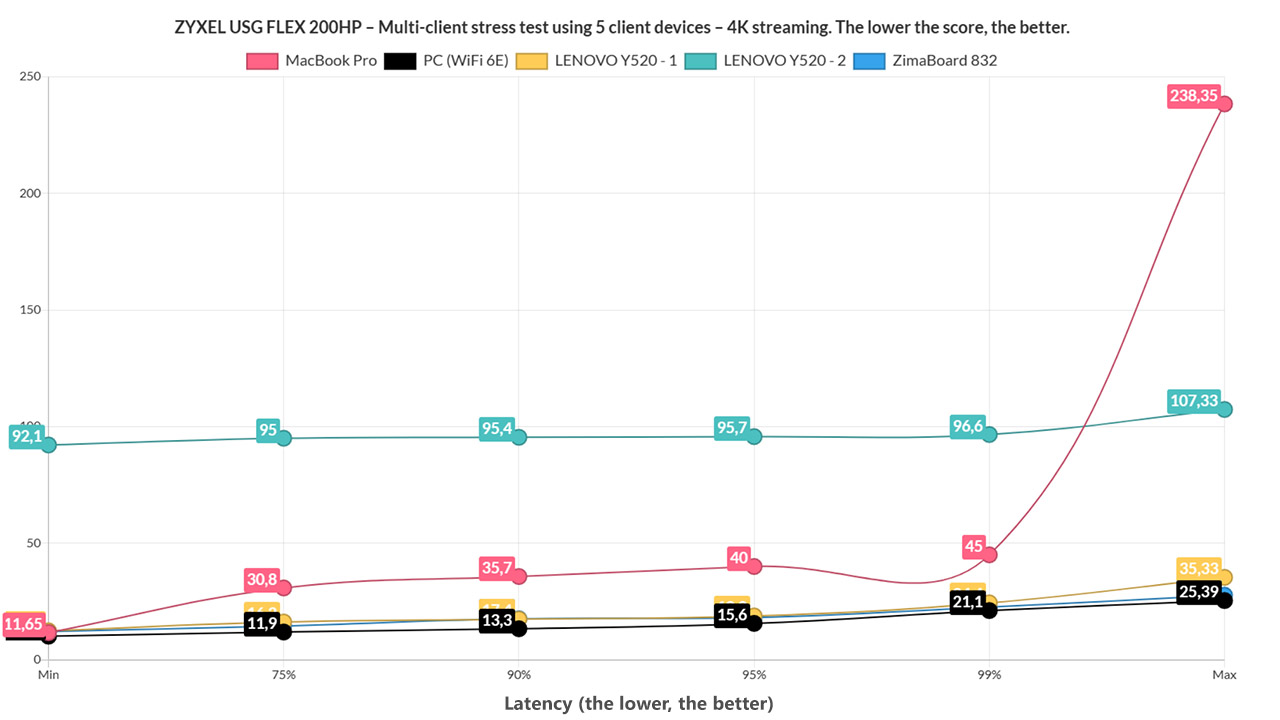
And, as you can see, the WiFi 6E PC (I called it like that since I also use it for WiFi testing, so it’s easy across reviews) performed really well alongside the ZimaBoard 832 and one of the two Lenovo Y520. I did see a spike above 200ms on the MacBook, but the average remained very low at 26.7ms, so I suppose it’s negligible. What was curious was the second Y520 laptop which constantly stayed very close to 100ms (and a single spike above it). What does all this mean? It means that streaming 4K at the same time on five client devices should be handled by the ZYXEL USG FLEX 200HP without issues.
And I suppose it also puts to rest the idea that this test only checks the performance of the client Ethernet adapters. I am not saying that it can’t be a decisive factor, because as you will soon see, it can be up to a point. But at the same time, two identical computer did behave differently, so the QoS and the overall load on the gateway is equally as important, if not more. I didn’t bother with 1080p considering that it handled 4K so well, so I added browsing in the mix on all five client devices.
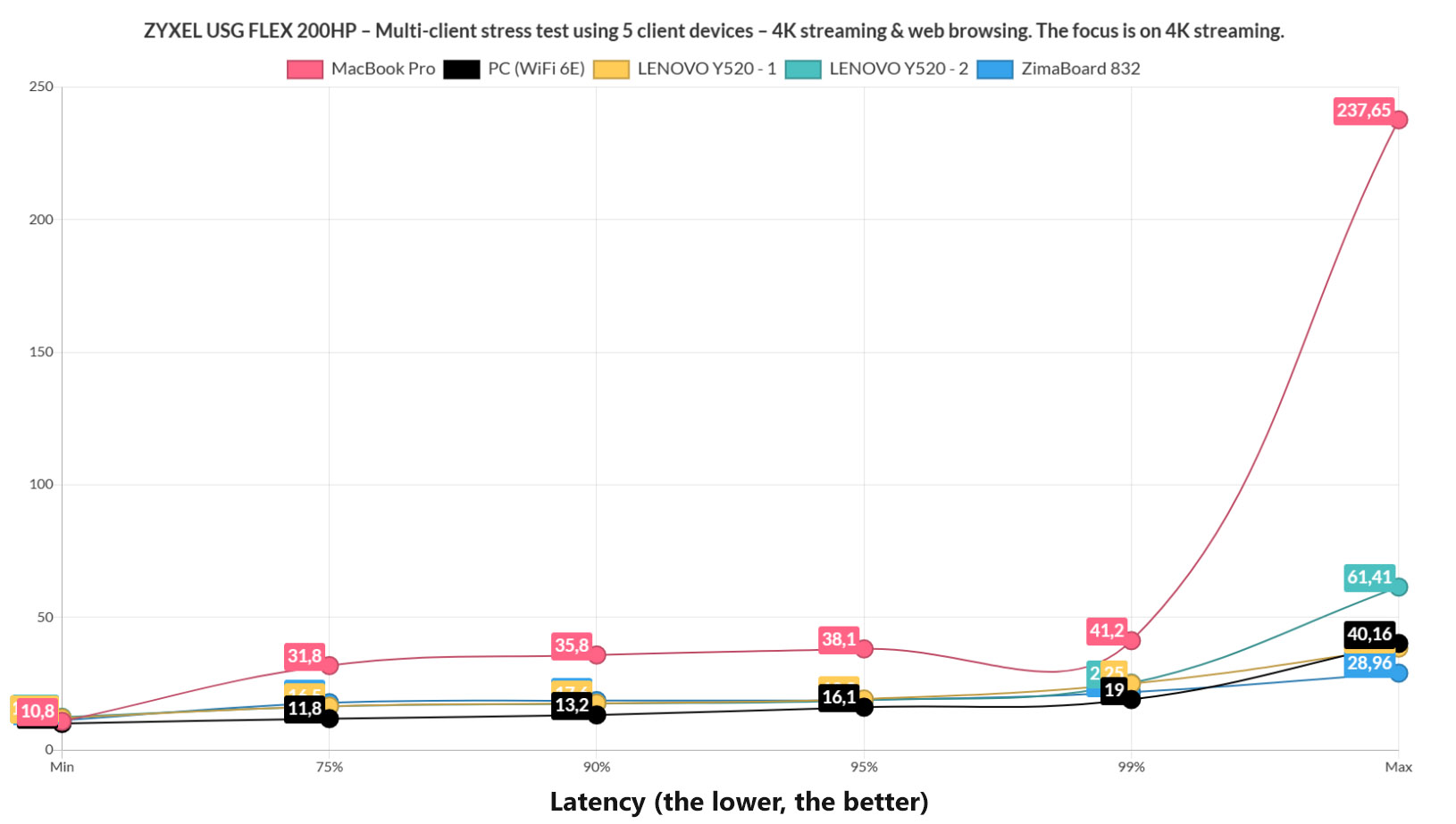
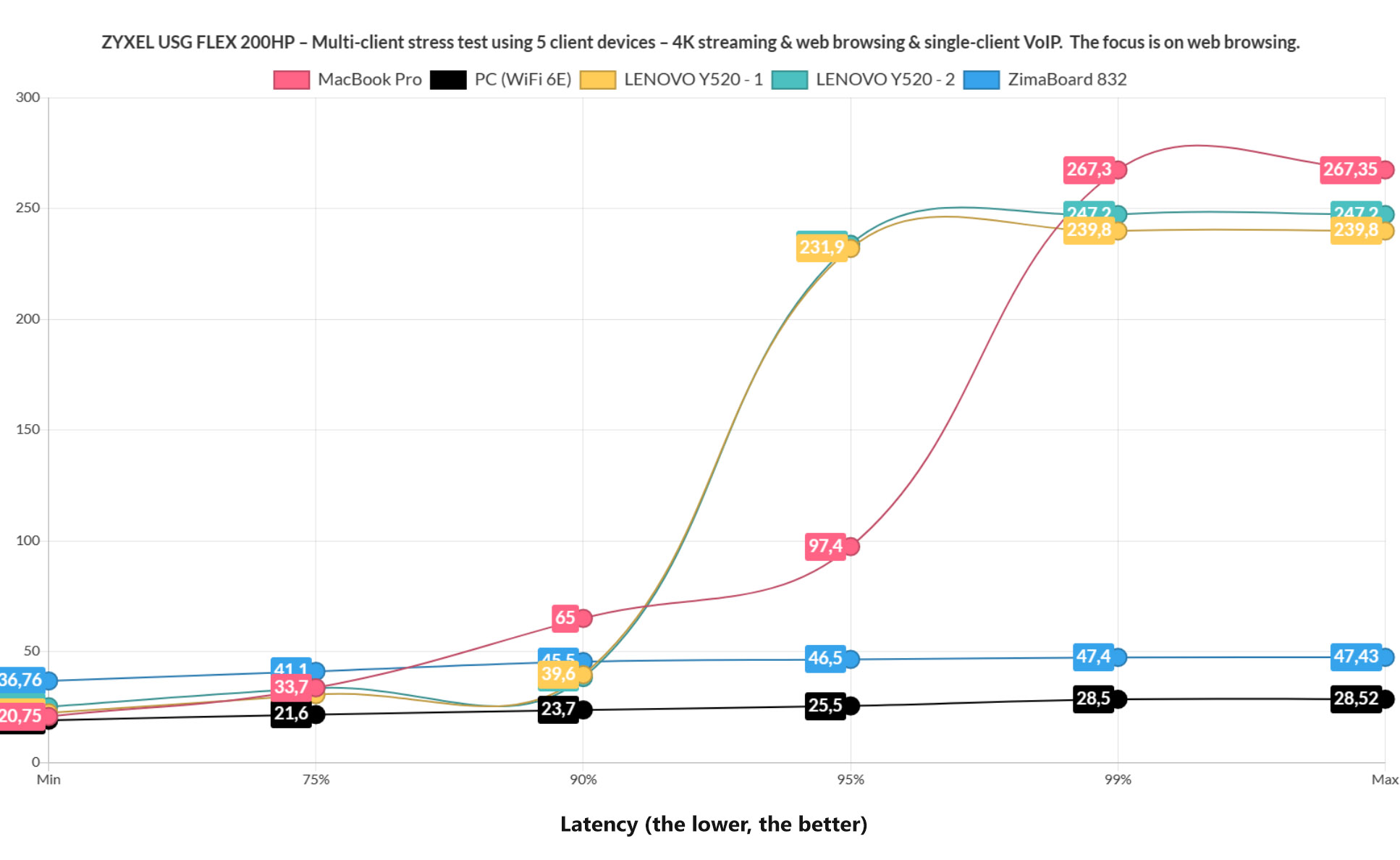
The throughput is limited to 1Mbps and we also added 500ms of jitter in order to simulate a fairly real browsing experience, a very, very intense one. It did have a slight impact on the latency across all client devices, although pretty much all remained underneath the 100ms for the most part.
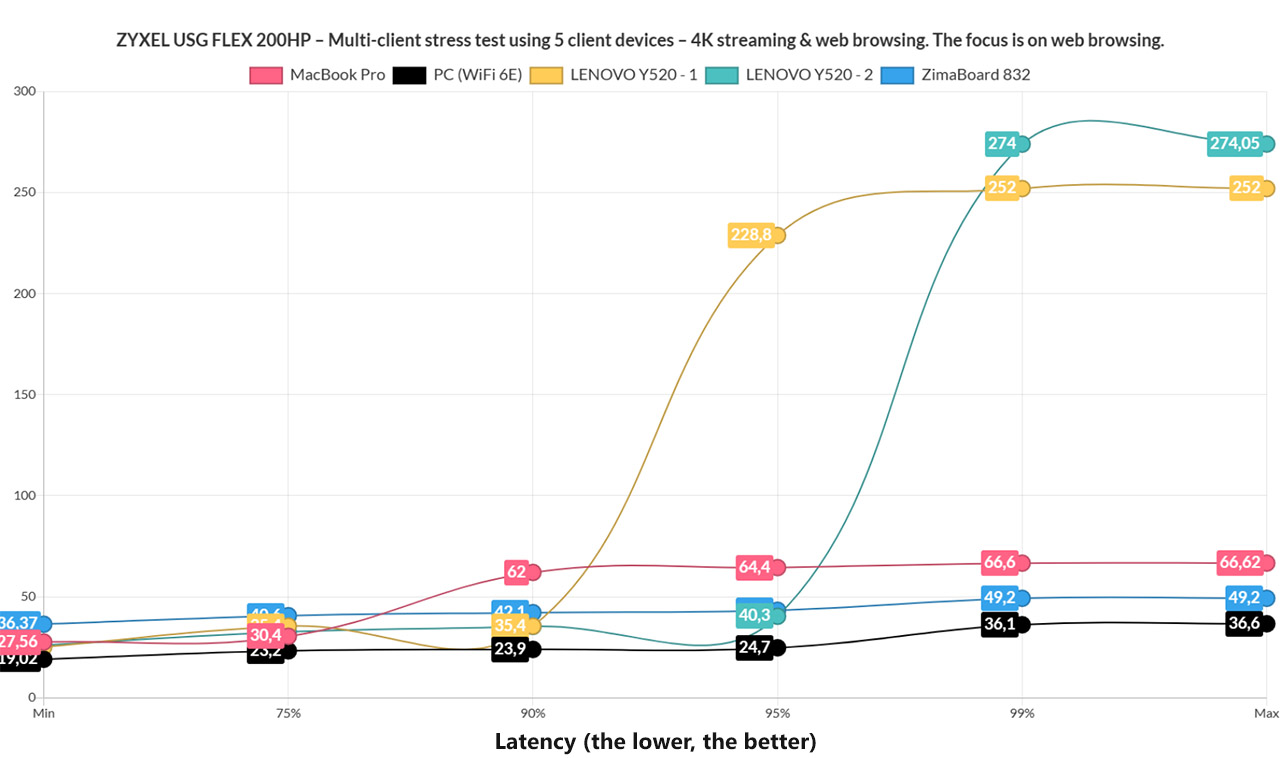
I suspect that the spike on the MacBook Pro continues to happen due to the QNAP 5GbE adapter. For browsing, I decided that a 1500ms limit is decent, although you can correct me if I am wrong. And all client devices remained underneath this limit without getting anywhere near it. And again, the Y520 twins show very different numbers.
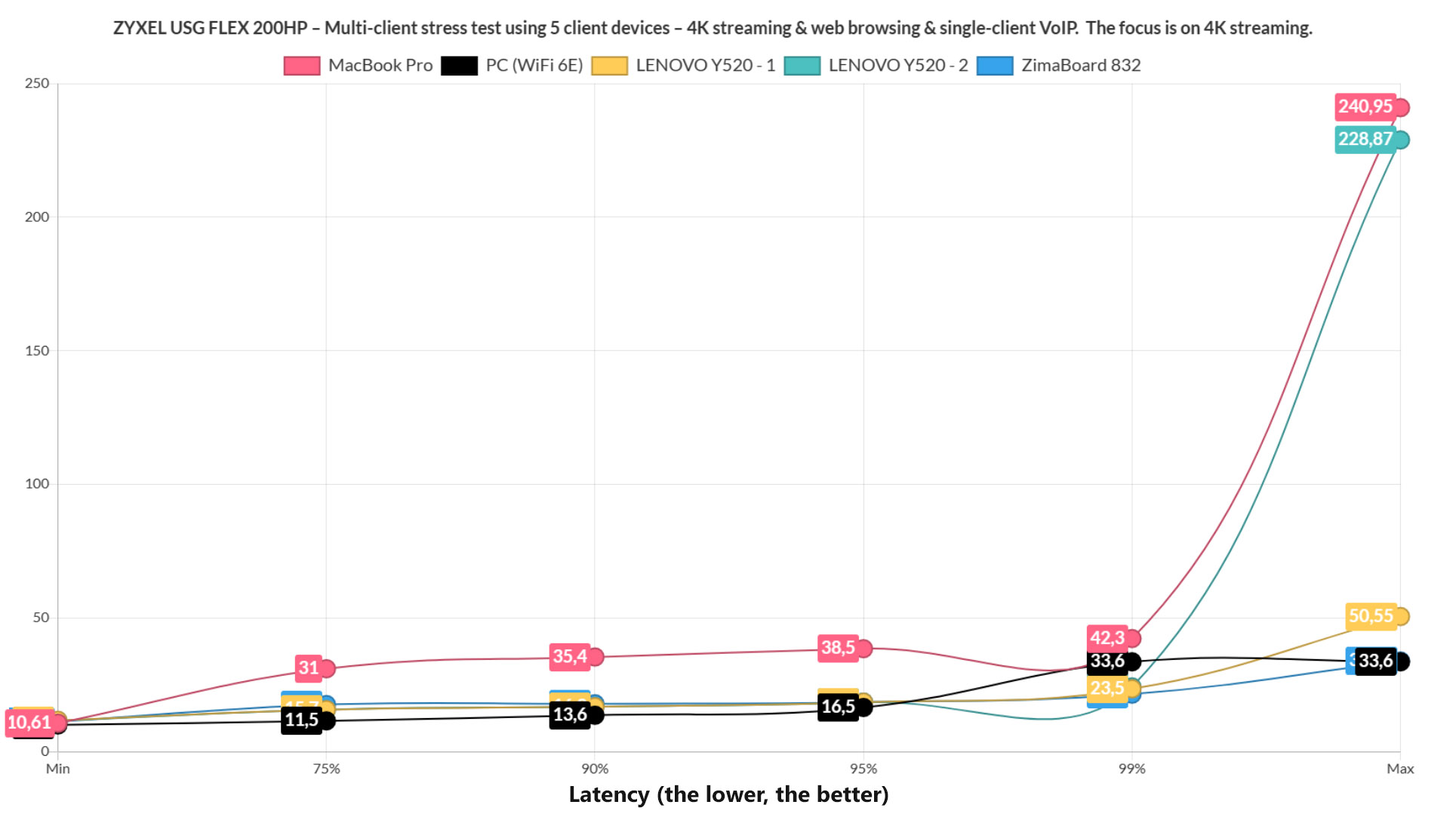
Lastly, I added VoIP in the mix, although just on a single client device. And it seems to have caused some very mild upsets. Browsing-wise, everything is within norm, but the 4K streaming did show some latency spikes on a couple of client devices, but again, it seems to be once in a while, so I suppose it can be seen as negligible. Overall, I think that the ZYXEL USG FLEX 200HP did very well, which was to be expected considering the price tag of the device.
The Nebula Cloud Platform (NCC)
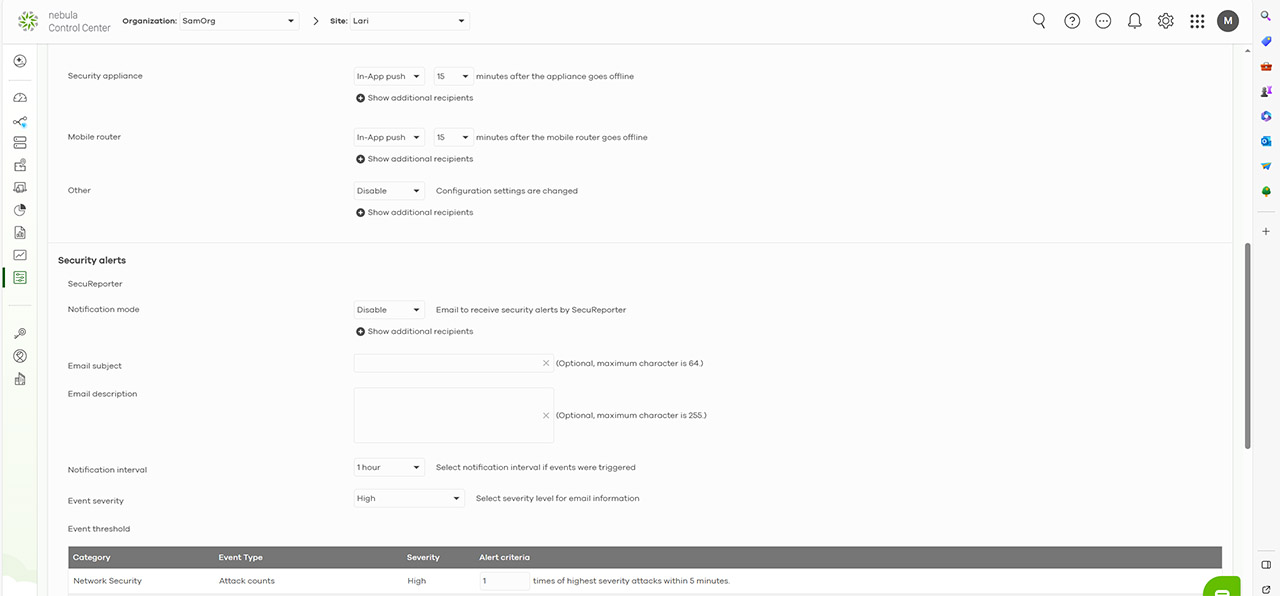
The installation wizard will make sure that the ZYXEL USG FLEX 200HP is paired to the Nebula Cloud platform for the beginning and to access it, you do need to go to nebula.zyxel.com and have an account. Then, after choosing the Organization, it is possible to monitor and configure your network. I expected that most if not all of the features and options found on the local management platform to be found here as well, but that’s not really the case yet.
The Configure section will let you adjust the Alarms when the security features detect any intrusion. Even the Monitor section offer pretty much nothing for the gateway, with the focus being on APs and switches. the Dashboard will show all types of devices that are added to the network, along with various status info, and, if you click on the Firewall, it will take you to the Devices > Firewall section.
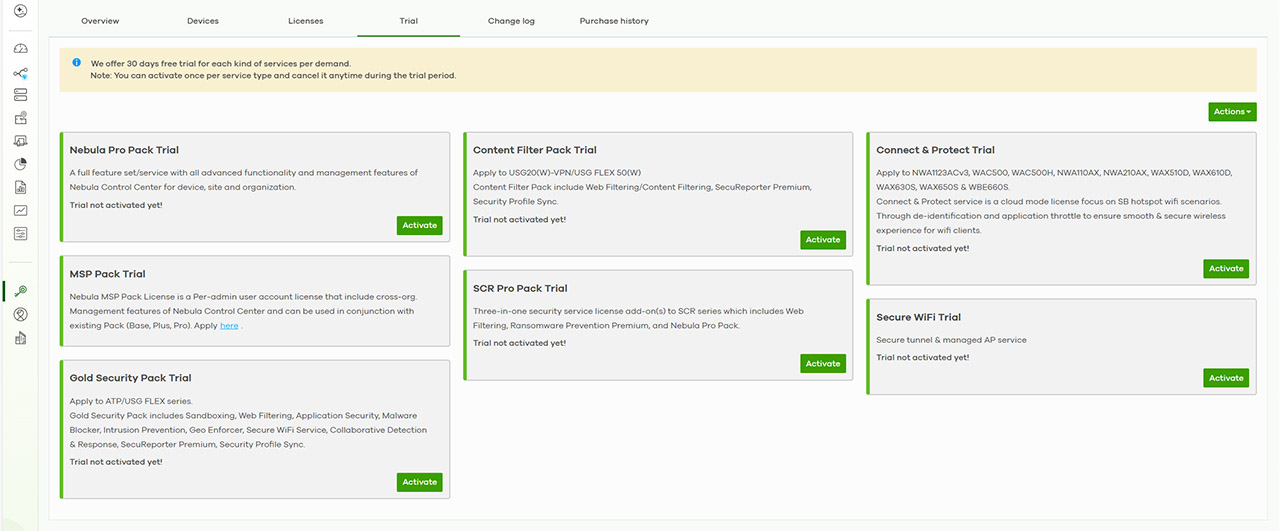
Here, you’re going to see even more info, including the location, as well some Live Tools, some which are part of a paid subscription: there’s Remote SSH and Remote configurator, both establishing a connection to a remote device via slightly different means. So, the point of the Nebula Cloud platform is to ensure that the org/site admin can have quick access to all the devices in the network.
And ZYXEL has worked hard at giving the admin lots of tools to diagnose network problems even if not on site.
Surely the integration with the on-site options is a working solution, especially since the limit is one firewall per site, but I do look forward to when Zyxel expands this limitation and provides a more robust configuration system on the Cloud platform as well.
The Conclusion
Hardware-wise, the ZYXEL USG FLEX 200HP is a complete improvement over the last generation and the addition of a PoE port is very much welcomed. Software-wise, again, things got better and we do get a very comprehensive local management platform which includes some advanced security options. But, do be aware that a lot of these features are only available with a subscription and they’re available both locally, as well as on the Cloud platform. That being said, if you have an SMB-level or even a larger network and prefer the Nebula ecosystem, then the ZYXEL USG FLEX 200HP is an excellent firewall gateway addition.
ZYXEL USG FLEX 200HP
Pros
- Robust design + possibility to rack mount the gateway.
- Quite a few security features + both local and Cloud management
- Performed really well in the multi-client stress test.
- The dual-WAN switch between links is quick.
- Good thermal management
Cons
- Need to create a new Organization to create a new Site.
- Can't completely remove the admin account.
- Only WRR available for multi-WAN

Mark is a graduate in Computer Science, having gathered valuable experience over the years working in IT as a programmer. Mark is also the main tech writer for MBReviews.com, covering not only his passion, the networking devices, but also other cool electronic gadgets that you may find useful for your every day life.