The Raspberry Pi Zero is currently the most affordable device from the Pi series and it was designed for both lighter projects where a Pi 3 B+ or Pi 4 would be severely underused and to help people in disadvantaged communities to build low-cost robots or to simply run a very basic OS. When I say affordable, I mean only $5 which is a ridiculous sum for the type of applications that it can run and, considering that I’ve been trying to find a reliable and cheap hardware-based alternative to the extension-based ad blockers, the Raspberry Pi Zero is probably the best way to run Pi-Hole on your network.
I did see some interesting functions implemented within the pcWRT‘s OpenWRT-based software, but, most consumer routers do not have in place any sort of ad-blocking abilities – those that do, it’s usually done via third-party software which will ask for a monthly pay and I know that the package is usually beefier, as it most likely also includes Parental Controls (which a lot of the WiFi systems shamelessly stripped in the first place) but, if there would be a welcomed addition, it would be Intrusion Prevention and the Intrusion Detection Systems, which, unfortunately do not run properly on less powerful routers in the first place.
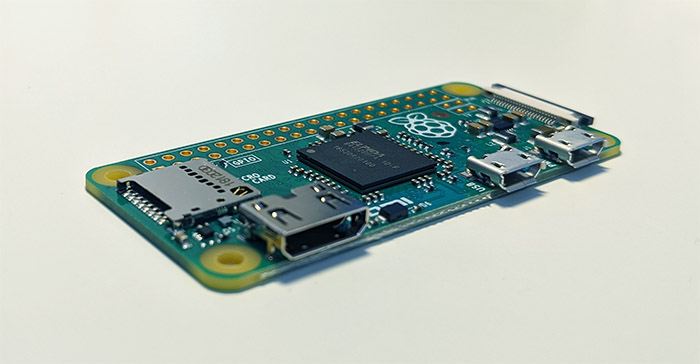
I know that the Pi-Hole does not require that many resources and people often joke about it being able to run on a potato, but, jokes aside, can it truly handle a 10+ clients network? The Raspberry Pi Zero is equipped with a Broadcom BCM2835 processor (1GHz ARM11), 512 MB of LPDDR2 SDRAM, a mini-HDMI port for 1080p video output (60fps), some microUSB ports and an unpopulated 40-pin GPIO header (you will have to solder a male GIPO header if you want to add any accessories, such as a fan), so it does meet the needed requirements and it should be powerful enough to handle Pi-Hole even with a large number of clients.
To see if I encounter any issues, I decided to install Pi-Hole on a non-wireless Pi Zero (there is a W -wireless- variant that costs a bit more, specifically, about $5 more), so, I followed the same steps that I did when I installed Pi-Hole on a Raspberry Pi 4 2GB: insert an SD card in a computer to install Raspbian (still preferred the headless version) using Etcher and then, after inserting the SD card into the Pi Zero, I used PUTTY to SSH into the device after it was connected to the router (you will need to know the IP address of the PI in order to do so).
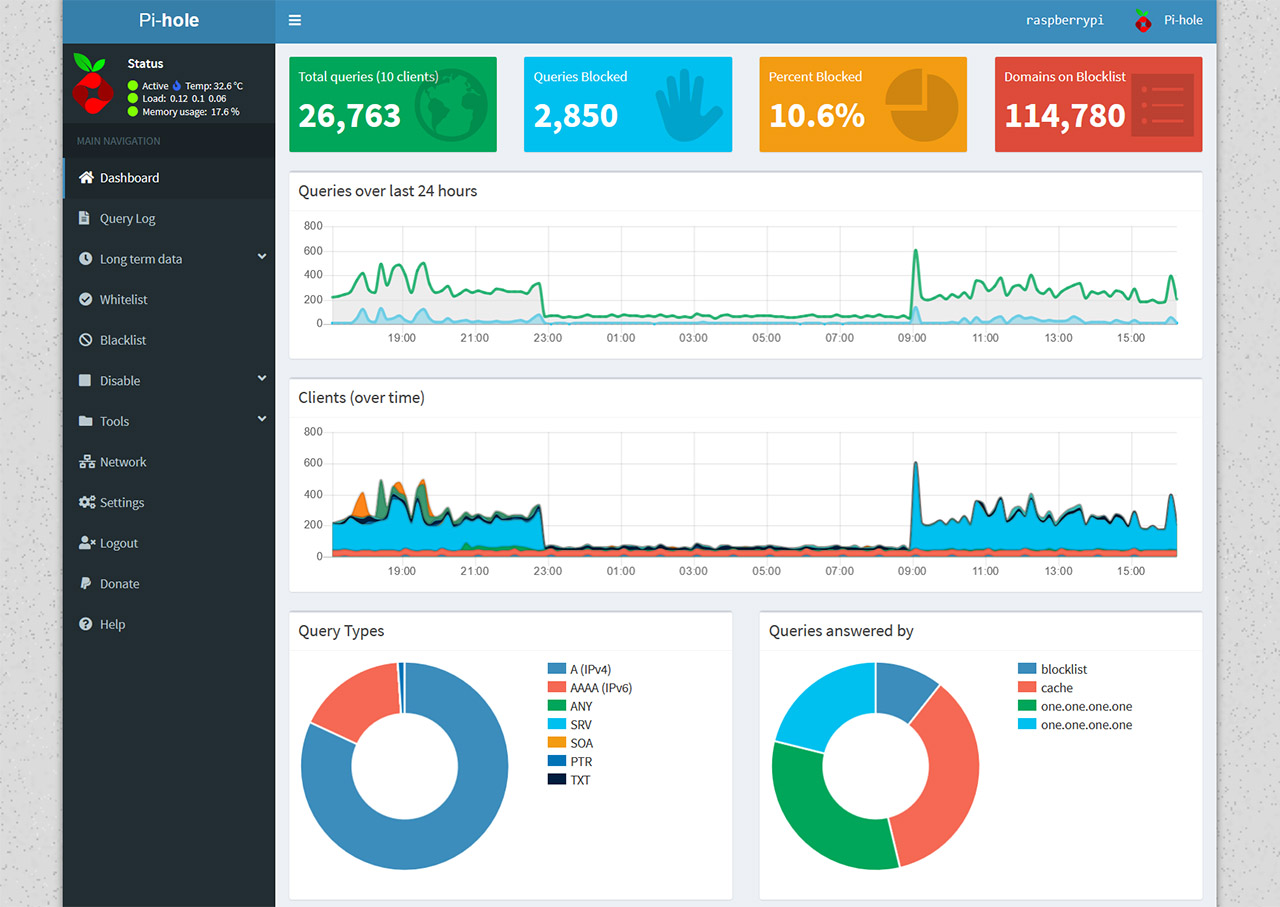
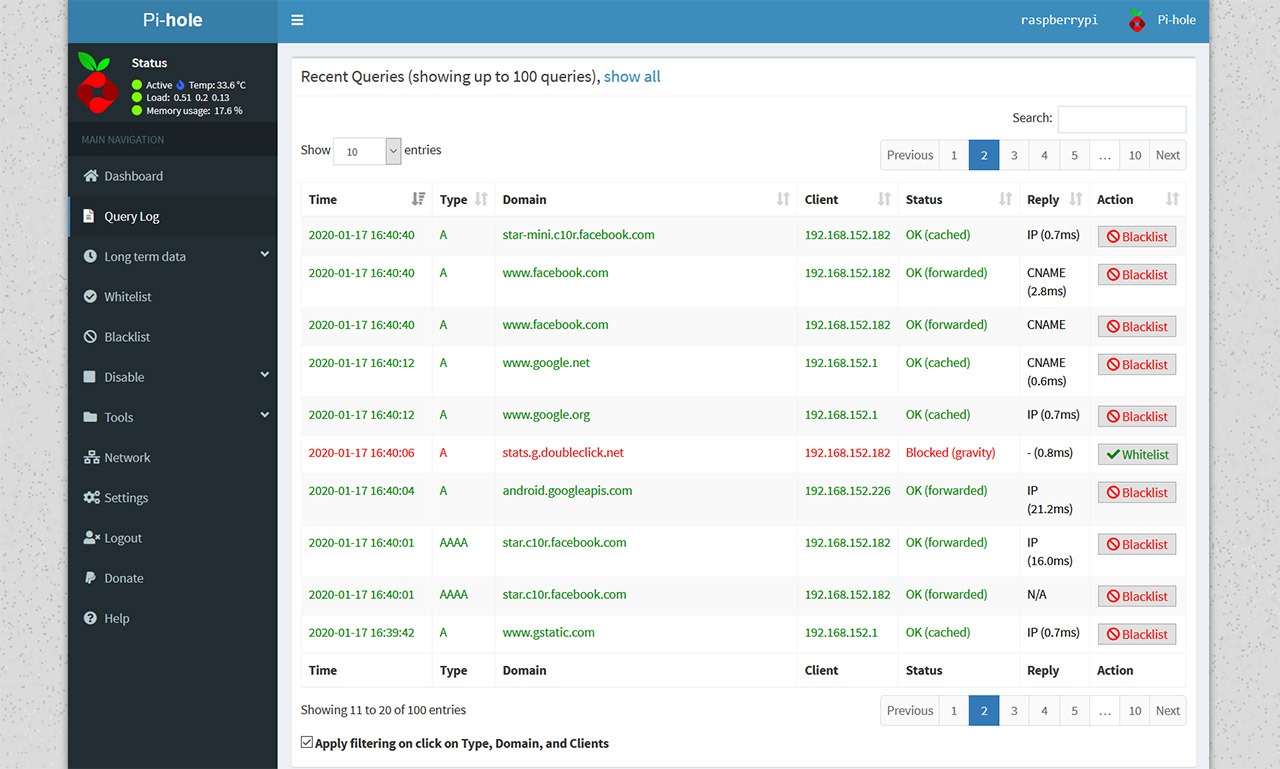
Afterwards, after changing the password and removing the default user, I entered ‘curl -sSL https://install.pi-hole.net | bash’ and followed the instructions until Pi-Hole finished installing: you can read a more detailed guide here, when I installed Pi-Hole on the Raspberry Pi 4. Lastly, you will have to point the DNS address of the router towards the Pi-Hole and the location of this setting differs on every router. After doing so, you can enter pi.hole in the URL of your favorite browser and navigate the GUI. If you’re a thorough person, then you may immediately notice that the Query Log will not show the blocked domains by client, instead, it’s either localhost or the IP address of the router.
In order to show each client with its own traffic, things can be easy or incredibly difficult, depending on the router brand, but I have explored some ways to do it using the Google WiFi and the Netgear Orbi, which are more difficult to achieve, so you can check them out if you need a guide (it’s worth noting that adjustment has proven to be very easy to do on an AmpliFi HD, so kudos to Ubiquiti). After that’s done, the experience should be identical to the Raspberry Pi 4, but is it though?
I have seen some network hiccups in the first couple of days after I added it to my current router (which, is still the AmpliFi HD GE – I find the screen and the bottom LED just too cool to install any other router) and I had to reconnect to the WiFi network once and the problems seem to have disappeared indefinitely (some mildly radical network changes such as this one can sometimes require the clients to reconnect, so it’s not that uncommon to experience some issues prior to it). Other than that, the experience is identical on every Pi and you do get to block or whitelist specific domains and use preexisting lists which are quite efficient at blocking the most common ad domains on the Internet.
Be aware that Pi-Hole does not work in the same manner as the browser-based ad block extensions, where you can whitelist or block a specific website entirely or a single page and, instead, Pi-Hole whitelists an entire domain, so, anytime you encounter that ad domain on any website, you will be able to see it (or, if you block it, it’s going to disappear from every website you visit).
This can be a bit annoying when you want to whitelist a website to show gratitude to the content creator, but Pi-Hole was never intended to be that surgical and instead, the point was to block certain domains that are known to cause harm (such as malware) or major annoyance (those dreaded pop-ups), not to remove all ads from the Internet. That being said, the Raspberry Pi Zero is more than capable of running Pi-Hole and, for $5, it’s more than worth it for not only blocking harmful ads, but to also be a starting platform for trying other, possibly more complex applications that were previously suitable to run on more expensive hardware.

Mark is a graduate in Computer Science, having gathered valuable experience over the years working in IT as a programmer. Mark is also the main tech writer for MBReviews.com, covering not only his passion, the networking devices, but also other cool electronic gadgets that you may find useful for your every day life.